Prestashop unremoved install directory risks
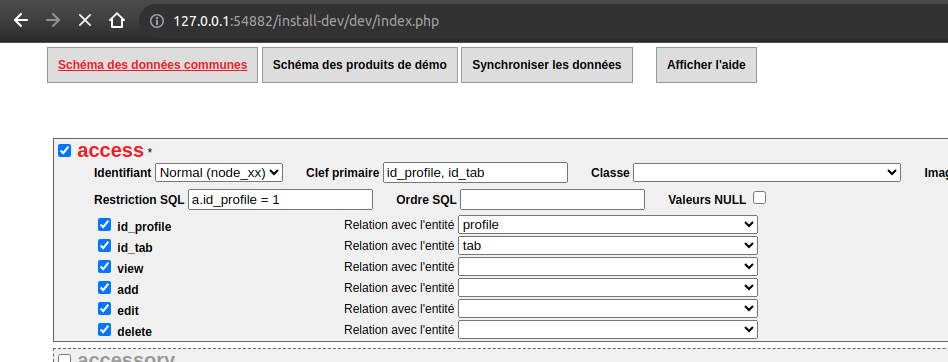
Prestashop installation directory must be deleted after a successful installation. It should not be renamed, as the remaining directory can contain code that is exploitable if publicly accessible, such as:
- tool to sync information in database
- tool to extract db information in xml files
Understanding how renamed install directories become vulnerable to discovery
We have seen scan from bots that try to access several CMS known sensible directories. The following list is not exhaustive but give an example of directories scanned
__install
_install
instalold
install.bck
install.back
install123
install.old
install0
install.inc
install_todelete
What should I do
Check your Prestashop installation and delete the install directory. Enable a check on your monitoring platform to detect such directory or ask your hosting company to detect and notify you if an install directory is detected.
If you have an install directory at the root of your Prestashop installation, you should search your access log to check if the directory was accessed.
DISCLAIMER: The French Association Friends Of Presta (FOP) acts as an intermediary to help hosting this advisory. While we strive to ensure the information and advice provided are accurate, FOP cannot be held liable for any consequences arising from reported vulnerabilities or any subsequent actions taken.
This advisory and patch is licensed under CC BY-SA 4.0